self-signed certificate for remote desktopI have two workstation connected in workgroup serverless. Show
How do I configure the two workstation in order to connect with the new self-signed certificate? Thanks Giorgio.M Comment Comment Show 0 Comment 5 |1600 characters needed characters left characters exceeded ▼
Attachments: Up to 10 attachments (including images) can be used with a maximum of 3.0 MiB each and 30.0 MiB total. Jingruihan-MSFT answered • Mar 16, '21 | Jingruihan-MSFT commented • Mar 22, '21 In your position, I'd like recommend you add certificates to the Trusted Root Certification Authorities store for a local computer. In other words, you have to import the self-signed certificates to Trusted Root Certification Authorities store on the client workstation. Comment Comment · Show 5 Comment 5 |1600 characters needed characters left characters exceeded ▼
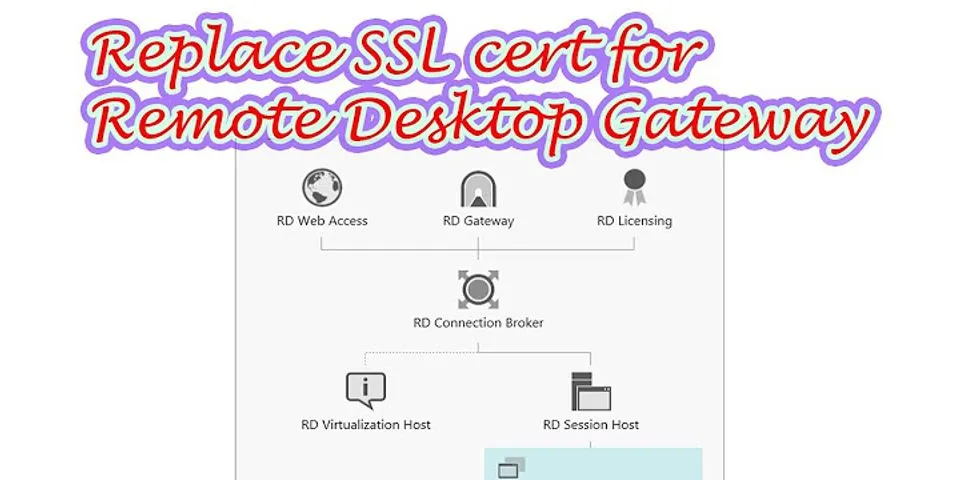
Attachments: Up to 10 attachments (including images) can be used with a maximum of 3.0 MiB each and 30.0 MiB total. GiorgioM-4220 · Mar 17, 2021 at 08:03 AM Thanks for your answer, but I need to use a self signed certificate and I would like understand the procedure to configure the two workstation in order to use the new certificate 0 Votes 0 · Jingruihan-MSFT GiorgioM-4220 · Mar 18, 2021 at 02:53 AM Hi Giorgio.M As you said it's worked that use self-signed certificates for workgroup serverless purposes. It is necessary to install the certificate on all of the RD Session Host servers manually. This is because there is no way to do this using the Server Manager GUI, and the certificate is not applied to session host servers automatically when configuring the certificates on the other roles. You may set the certificate using wmi. Please import the certificate and its private key into each RDSH server's Local Computer\Personal store (using Certificates mmc snapin), then run the following command in an administrator command prompt: I hope this would be some help. 1 Vote 1 · GiorgioM-4220 Jingruihan-MSFT · Mar 19, 2021 at 08:41 AM Hi Jingruihan, Thanks Bye 0 Votes 0 · GiorgioM-4220 Jingruihan-MSFT · Mar 19, 2021 at 10:26 AM Thanks @JimmyYang-MSFT, Thanks Bye 0 Votes 0 · [Forum FAQ] How to setup Self-Signed Certificate for RDSCreating RDP CertificatesBy Jake Grandlienard | March 5, 2020 | 19  In a previous blog on Object Identifiers (OID) in PKI, I mentioned creating a certificate template for Remote Desktop Connection (RDP). In this blog, I will show how to create the template, why the OID and extensions are important, and how to implement it and remove self-signed certificate warnings Important Note
Why Issue RDP Certificates? There are multiple reasons to issue RDP certificates from a PKI. The most noticeable is the warning displayed when making an RDP connection to a server or client. Upon the first RDP connection, servers and clients generate a self-signed certificate, which are not trusted so the warning is displayed.  Clicking Yes, to connect sets a bad precedent, especially when checking the box to not be notified again. In servers and clients prior to Windows 8.1 and Server 2012R2, the self-signed certificates were issued based on a SHA1, until an update when they started issuing SHA2 based self-signed. After following these steps, clients and servers the GPO is Current Policies & Corresponding OIDs To view the policies and OID list, open the certificate templates console (certtmpl.msc), then right click on the console root at the top left and select “View Object Identifiers...  The highlighted policy above is Microsoft’s OID designation Creating Remote To create the policy, open certificate templates console (certtmpl.msc) Utilizing the New Certificate Template Publish the new RDP template to a certificate authority. For servers to automatically enroll and stop generating and using self-signed certificates a GPO must be configured. The GPO settings are located under: Computer Configuration, Policies, Administrative Templates, Windows Components, Remote Desktop Services, Remote Desktop Session Host, Security, Server Authentication certificate template. Update the policy with the template name or OID of the RDP certificate template and select the enable radio button then OK. When the GPO refresh applies to targeted servers they will enroll for the new certificate and use it for RDP connections.   When setting the Certificate Template Name for RDP template in the GPO, rather than using the template name, the templates OID may also be used. The OID is shown under the Extension tab in the Certificate Template Information or via Certutil: Certutil -adtemplate -v “<template name>”. Posted in OID, PKI, RDP ← Accessing and using certificate private keys in .NET Framework/.NET CorePKI Solutions Webinar Series →  About Jake GrandlienardJacob Grandlienard brings more than 19 years of industry experience as a senior level engineer. He has spent the past 10 years designing, leading, and training clients in Public Key Infrastructure (PKI) implementations for medium to enterprise-scale Fortune 500 companies. He specializes in PKI implementations of Microsoft-based identity solutions, including Microsoft Active Directory Certificate Services (ADCS) as well as integration with other security and identity management technologies. Jacob is a subject matter expert in PKI, mobile device management software, smart card management software, and Hardware Security Module (HSM) integration. View all posts by Jake Grandlienard → Certificate Template for RDS



Click Add to include the following


 Resolution
This article describes a possible Microsoft® Remote Desktop Protocol (RDP) connection issue and the resolution. Issue: Connection failuresRDP connections begin to fail with no apparent cause. SymptomsThis issue might have the following symptoms:
CauseThe following events could cause this issue:
ResolutionUse the following steps to resolve this issue:
Use the Feedback tab to make any comments or ask questions. You can also start a conversation with us. ©2020 Rackspace US, Inc. Except where otherwise noted, content on this site is licensed under a Creative Commons Attribution-NonCommercial-NoDerivs 3.0 Unported License  See license specifics and DISCLAIMER RDP Certificate Template1. On your Microsoft certificate authority server open the Certificate Templates console. 2. Expand the CA and right click on Certificate Templates, then select Manage. 3. Right click on the Computer template and select Duplicate. 4. Change the template display name to RemoteDesktopComputer (no spaces). Verify the Template Name is exactly the same (no spaces). You can use a different name if you want, but both fields must match exactly. Change the validity period to match your company policy.  5. Now we need to create an application policy to limit the usage to RDS authentication, then remove the other application uses for the certificate. On the Extensions tab click on Application Policies then click on Edit. 6. Click on Add, then click on New.Set the value of Name to Remote Desktop Authentication. Change the object identifier (OID) to 1.3.6.1.4.1.311.54.1.2.  7. From the Application Policies list, select Remote Desktop Authenticationand click OK. 8. Back on the certificate template properties, remove all other entries. Only Remote Desktop Authentication should be present.  9. You probably want to secure your domain controllers as well, so for that we need to modify the security setting on the template. Open the Security tab and add the group Domain Controllers and give the group Enroll (not Autoenroll). Close out the certificate.  10. Open the MMC snap-in for managing your Certificate Authority and locate the Certificate Templates node. Right click, select New, then Certificate Template to Issue. Choose the RemoteDesktopComputer template.  |